# Plug-in description
The JWT verification plug-in does not generate a token. The token is generated by the business. The plug-in only verifies that the token is legal. Supports verification of tokens using the following algorithms:
-HS256 -HS384 -HS512 -RS256 -RS384 -RS512 -ES256 -ES256K -ES384 -ES512
# Instructions for use
When a route requires JWT verification, you can add the JWT plug-in to the route details page for verification. The configuration is as follows:
# Global configuration
Support global default key configuration for plug-ins in Gateway Management->Plug-in Management. The custom configuration format is as follows:
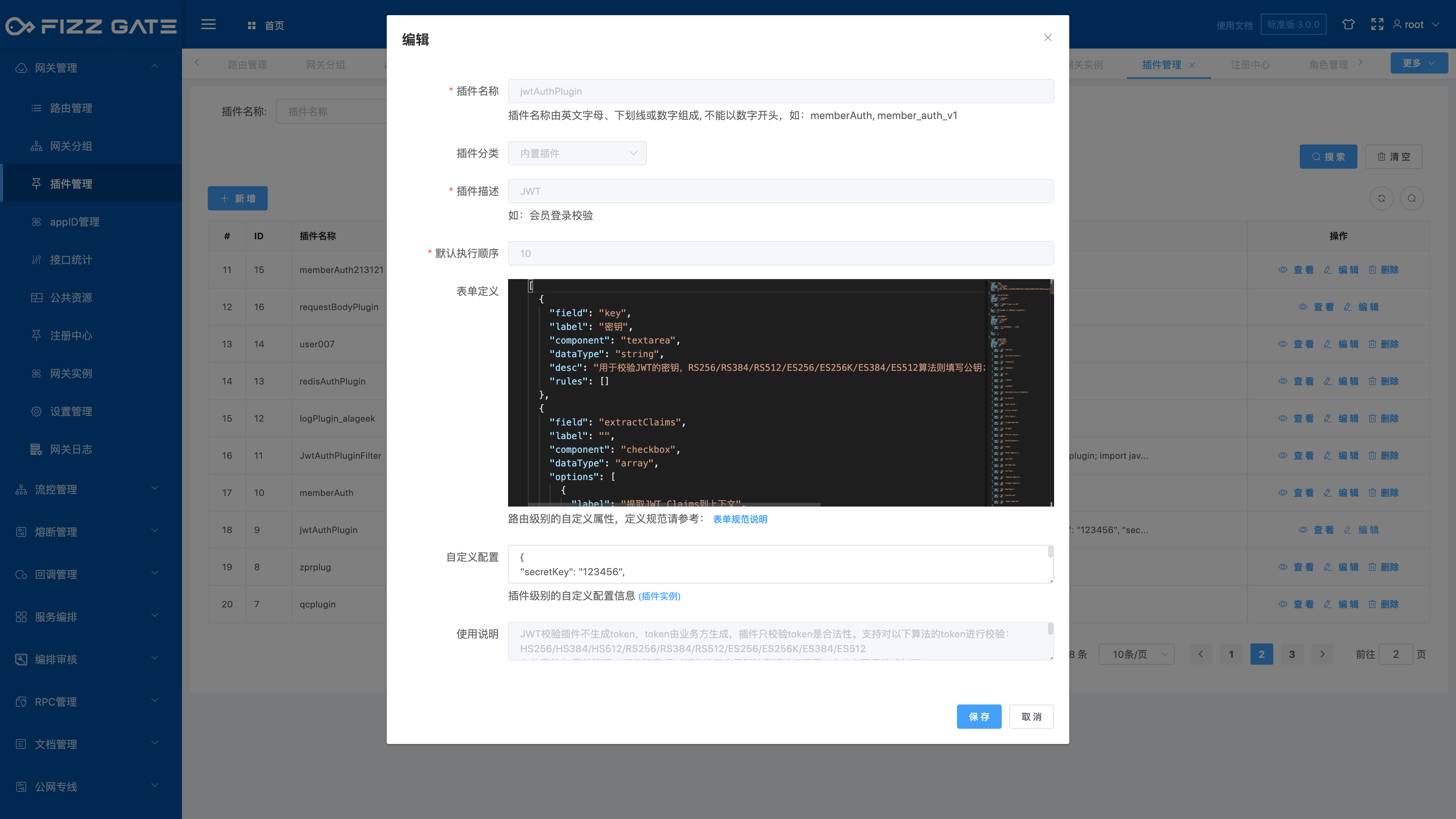
{
"secretKey": "123456",
"secretKey_desc": "secret key for HS256/HS384/HS512 Algorithm",
"publicKey": "-----BEGIN PUBLIC KEY-----
MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAuGbXWiK3dQTyCbX5xdE4
yCuYp0AF2d15Qq1JSXT/lx8CEcXb9RbDddl8jGDv+spi5qPa8qEHiK7FwV2KpRE9
83wGPnYsAm9BxLFb4YrLYcDFOIGULuk2FtrPS512Qea1bXASuvYXEpQNpGbnTGVs
WXI9C+yjHztqyL2h8P6mlThPY9E9ue2fCqdgixfTFIF9Dm4SLHbphUS2iw7w1JgT
69s7of9+I9l5lsJ9cozf1rxrXX4V1u/SotUuNB3Fp8oB4C1fLBEhSlMcUJirz1E8
AziMCxS+VrRPDM+zfvpIJg3JljAh3PJHDiLu902v9w+Iplu1WyoB2aPfitxEhRN0
YwIDAQAB
-----END PUBLIC KEY-----",
"publicKey_desc": "public key for RS256/RS384/RS512/ES256/ES256K/ES384/ES512 Algorithm"
}
- secretKey is the key used by the HS256/HS384/HS512 algorithm. If it is not these algorithms, it can be left blank.
- publicKey is the public key used by the RS256/RS384/RS512/ES256/ES256K/ES384/ES512 algorithm. If it is not one of these algorithms, it can be left blank.
- secretKey_desc description field
- publicKey_desc description field
Routing-level key configuration has a higher priority than global keys. It is recommended to configure global keys.
# Routing level configuration
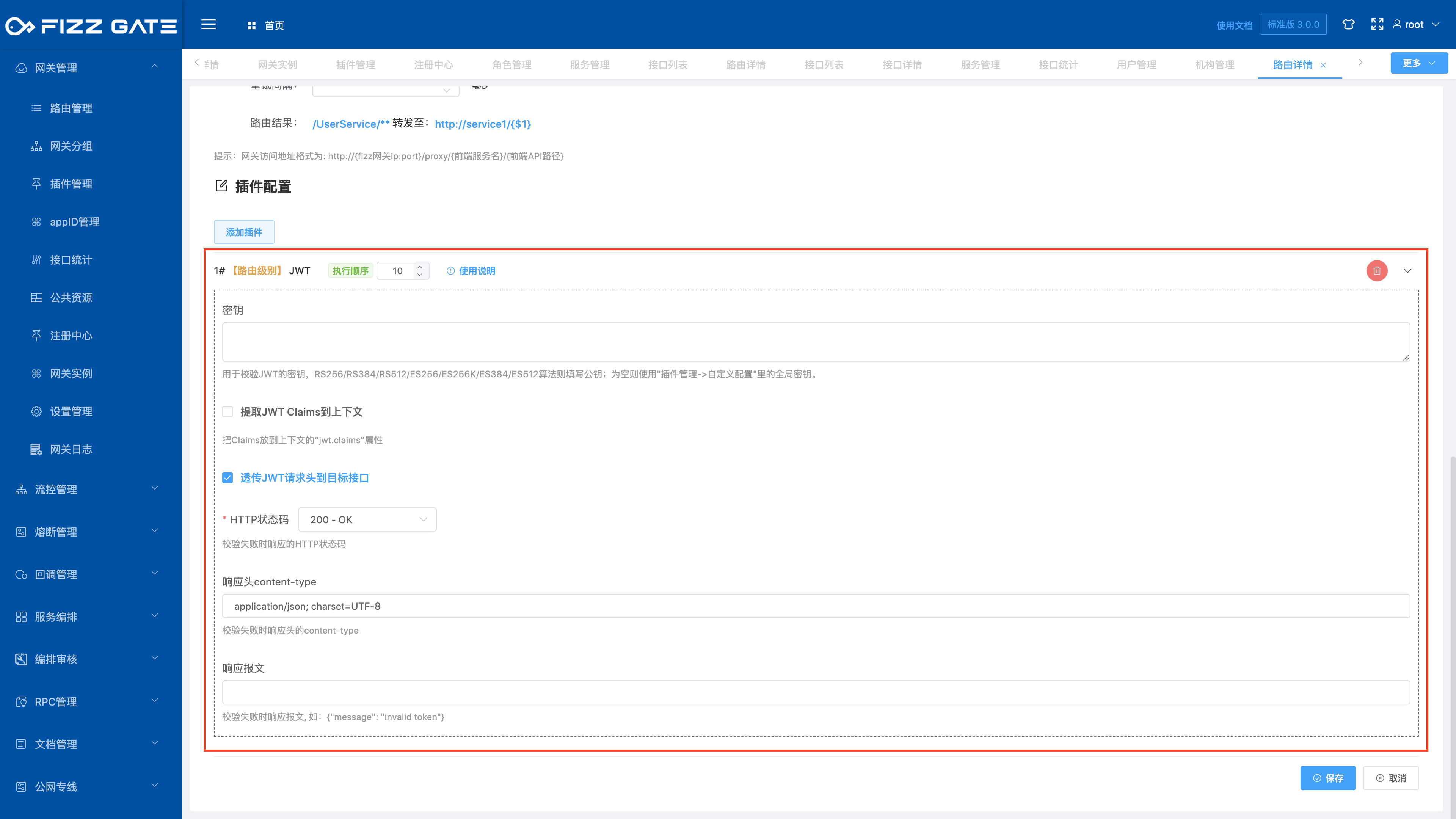
Key: If you have configured a global key configuration, you can leave it blank. If you do not configure a global key, each routing JWT plug-in needs to configure a key. When the JWT uses the HS256/HS384/HS512 algorithm, fill in the key to generate the token. When the JWT uses the RS256/RS384/RS512/ES256/ES256K/ES384/ES512 algorithm, fill in the public key (the public key is used to verify the token , the private key is used to generate the token).
You can customize the response message and HTTP status code when the token verification fails.
Extracting JWT Claims into the context is only used for secondary development and is not currently used.
# Caller passes parameters
The caller passes the Authorization request header when calling the interface, the format is: Authorization=Bearer token
Example:
Authorization=Bearer eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOiIxMjM0NTY3ODkwIiwibmFtZSI6IkpvaG4gRG9lIiwiaWF0IjoxNTE2MjM5MDIyfQ.keH6T3x1z7mmhKL1T3r9sQdAxxd zB6siemGMr_6ZOwU
